DDoS: The Digital Siege | Vibepedia
A DDoS attack, short for Distributed Denial-of-Service, is a cyberattack where an attacker overwhelms a targeted system, such as a website or network, with a…
Contents
- 🔒 Introduction to DDoS
- 📊 Types of DDoS Attacks
- 🚫 Understanding Denial of Service
- 🌐 Network Flooding
- 📈 Amplification Attacks
- 🔍 Application Layer Attacks
- 🕵️♂️ Identifying and Mitigating DDoS
- 🚨 Real-World Examples of DDoS
- 🤝 Collaborative Defense Strategies
- 📊 Economic Impact of DDoS
- 🔮 Future of DDoS and Cybersecurity
- 📚 Conclusion and Recommendations
- Frequently Asked Questions
- Related Topics
Overview
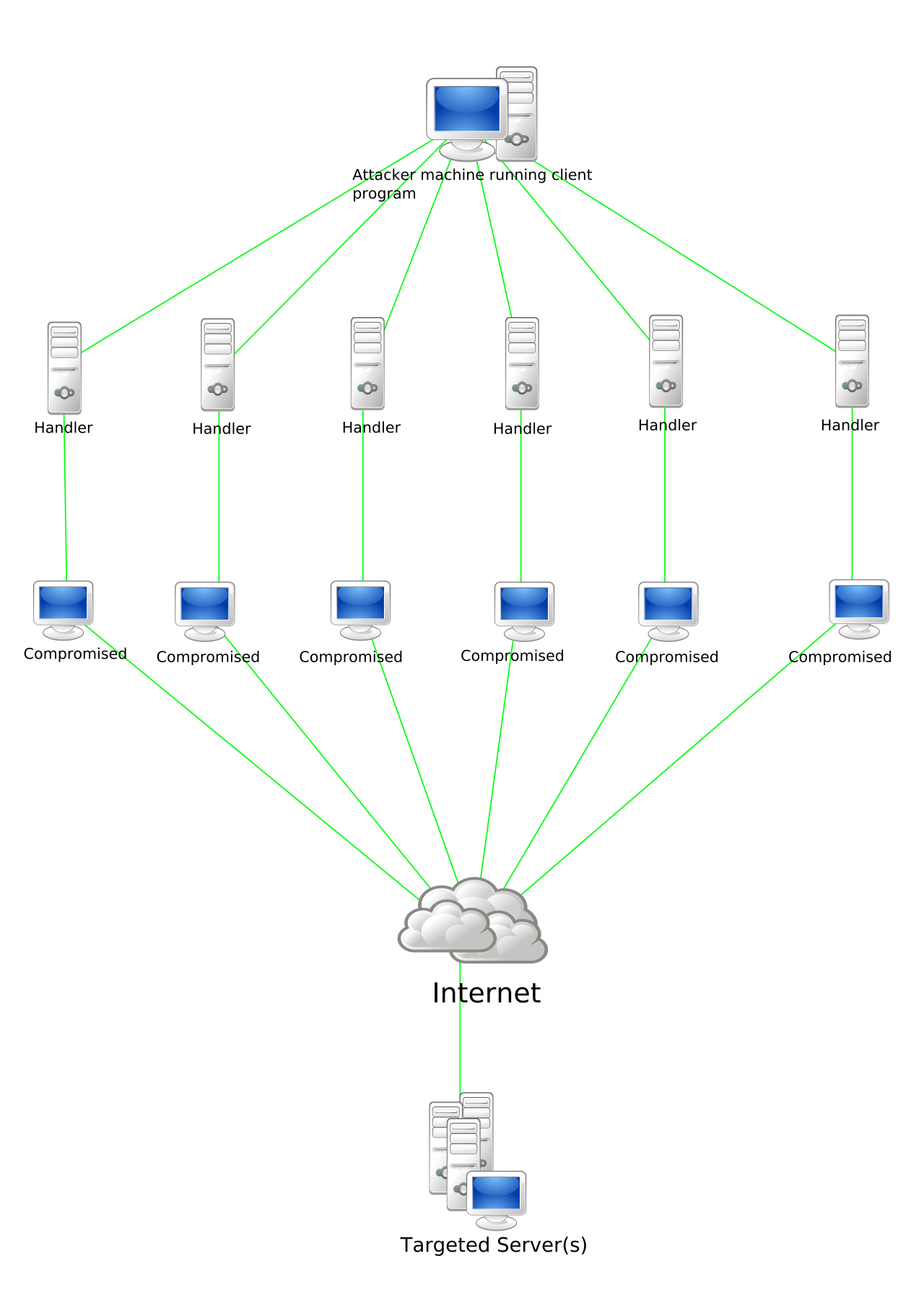
A DDoS attack, short for Distributed Denial-of-Service, is a cyberattack where an attacker overwhelms a targeted system, such as a website or network, with a flood of internet traffic from multiple sources. This can render the system unavailable to legitimate users, causing significant disruptions. According to a report by Akamai, the number of DDoS attacks increased by 14% in 2020, with the average attack size reaching 1.44 Gbps. The most notable DDoS attack to date is the 2016 Dyn cyberattack, which affected major websites such as Twitter, Netflix, and Amazon. As the threat landscape continues to evolve, it's essential to understand the motivations behind these attacks, which can range from hacktivism to extortion. With the rise of IoT devices, the potential for larger, more devastating attacks is becoming increasingly concerning, making it crucial for organizations to implement robust security measures to mitigate these threats.
🔒 Introduction to DDoS
The world of cybersecurity is filled with threats, but few are as devastating as a DDoS attack. A DDoS, or Distributed Denial of Service, attack is a type of cyberattack where an attacker attempts to make a machine or network resource unavailable to its intended users. This is typically accomplished by flooding the targeted machine or resource with superfluous requests, overloading systems and preventing legitimate requests from being fulfilled. As discussed in Cybersecurity 101, understanding the basics of DDoS is crucial in preventing and mitigating these types of attacks. For instance, Network Security measures can help detect and prevent DDoS attacks.
📊 Types of DDoS Attacks
There are several types of DDoS attacks, each with its own unique characteristics and goals. Volumetric DDoS attacks, for example, involve inundating a server with millions of requests to slow its performance. On the other hand, Application Layer DDoS attacks target specific applications or services, attempting to overwhelm them with a substantial amount of invalid data. As explained in DDoS Protection strategies, understanding the different types of DDoS attacks is essential in developing effective defense mechanisms. Furthermore, Incident Response plans can help organizations respond quickly and effectively to DDoS attacks.
🚫 Understanding Denial of Service
At its core, a denial of service attack is an attempt to disrupt the normal functioning of a network or system. This can be achieved through various means, including Network Flooding, where an attacker sends a large amount of traffic to a network in an attempt to overwhelm it. As discussed in Cyber Attack scenarios, denial of service attacks can have significant consequences, including loss of productivity and revenue. For example, DNS Security measures can help prevent DDoS attacks that target DNS servers. Additionally, Firewall Configuration can help block malicious traffic and prevent DDoS attacks.
🌐 Network Flooding
Network flooding is a common technique used in DDoS attacks. By sending a large amount of traffic to a network, an attacker can overwhelm the network's resources, making it difficult or impossible for legitimate traffic to get through. As explained in Network Architecture, understanding how networks are designed and configured is crucial in preventing and mitigating network flooding attacks. For instance, Load Balancing techniques can help distribute traffic across multiple servers, making it more difficult for attackers to overwhelm a single server. Moreover, Traffic Management strategies can help detect and prevent network flooding attacks.
📈 Amplification Attacks
Amplification attacks are another type of DDoS attack that involves exploiting vulnerabilities in network protocols to amplify traffic. As discussed in Amplification Attack scenarios, these types of attacks can be particularly devastating, as they can generate a large amount of traffic with relatively little effort. For example, DNS Amplification attacks involve exploiting DNS servers to amplify traffic, while NTP Amplification attacks involve exploiting NTP servers. Additionally, SSDP Amplification attacks involve exploiting SSDP servers to amplify traffic.
🔍 Application Layer Attacks
Application layer attacks, on the other hand, target specific applications or services, attempting to overwhelm them with a substantial amount of invalid data. As explained in Application Security, understanding the vulnerabilities of specific applications and services is crucial in preventing and mitigating these types of attacks. For instance, SQL Injection attacks involve injecting malicious SQL code into a web application's database, while Cross-Site Scripting attacks involve injecting malicious code into a web application. Furthermore, Input Validation techniques can help prevent application layer attacks by validating user input.
🕵️♂️ Identifying and Mitigating DDoS
Identifying and mitigating DDoS attacks requires a combination of technical expertise and strategic planning. As discussed in DDoS Mitigation strategies, organizations can use various techniques, such as Traffic Filtering and Rate Limiting, to detect and prevent DDoS attacks. Additionally, Incident Response Planning can help organizations respond quickly and effectively to DDoS attacks. For example, DDoS Detection tools can help identify DDoS attacks in real-time, while DDoS Response plans can help organizations respond quickly and effectively to DDoS attacks.
🚨 Real-World Examples of DDoS
Real-world examples of DDoS attacks include the Mirai Botnet attack, which targeted DNS provider Dyn and caused widespread outages. As explained in Botnet scenarios, these types of attacks can have significant consequences, including loss of productivity and revenue. For instance, DDoS Attack on Krebs involved a massive DDoS attack on security blogger Brian Krebs' website, while DDoS Attack on GitHub involved a massive DDoS attack on the GitHub platform. Furthermore, DDoS Attack on AWS involved a massive DDoS attack on Amazon Web Services.
🤝 Collaborative Defense Strategies
Collaborative defense strategies, such as Information Sharing and Threat Intelligence, can help organizations stay ahead of DDoS threats. As discussed in Cybersecurity Collaboration, sharing information and best practices can help organizations develop more effective defense mechanisms. For example, ISAC (Information Sharing and Analysis Center) can help organizations share information and best practices to prevent and mitigate DDoS attacks. Additionally, Cybersecurity Framework can help organizations develop a comprehensive cybersecurity strategy to prevent and mitigate DDoS attacks.
📊 Economic Impact of DDoS
The economic impact of DDoS attacks can be significant, with some estimates suggesting that the average cost of a DDoS attack is over $1 million. As explained in DDoS Cost, understanding the economic impact of DDoS attacks is crucial in developing effective defense mechanisms. For instance, DDoS Insurance can help organizations mitigate the financial impact of DDoS attacks, while DDoS Risk Management can help organizations assess and mitigate the risk of DDoS attacks. Furthermore, Cybersecurity Investment can help organizations invest in cybersecurity measures to prevent and mitigate DDoS attacks.
🔮 Future of DDoS and Cybersecurity
The future of DDoS and cybersecurity is uncertain, but one thing is clear: the threat landscape is evolving rapidly. As discussed in Cybersecurity Trends, organizations must stay ahead of emerging threats, such as IoT Security and AI-Powered DDoS. For example, IoT DDoS attacks involve using IoT devices to launch DDoS attacks, while AI DDoS attacks involve using AI algorithms to launch DDoS attacks. Additionally, Quantum Computing can help organizations develop more effective cybersecurity measures to prevent and mitigate DDoS attacks.
📚 Conclusion and Recommendations
In conclusion, DDoS attacks are a significant threat to organizations and individuals alike. As explained in Cybersecurity Best Practices, understanding the basics of DDoS and developing effective defense mechanisms is crucial in preventing and mitigating these types of attacks. For instance, DDoS Prevention strategies can help organizations prevent DDoS attacks, while DDoS Response Planning can help organizations respond quickly and effectively to DDoS attacks. Furthermore, Cybersecurity Awareness can help organizations raise awareness about the importance of cybersecurity and the threat of DDoS attacks.
Key Facts
- Year
- 2020
- Origin
- Early DDoS attacks date back to the 1990s, but the term 'DDoS' was first coined in 1999 by a group of computer scientists at the University of California, San Diego.
- Category
- Cybersecurity
- Type
- Cyber Threat
Frequently Asked Questions
What is a DDoS attack?
A DDoS, or Distributed Denial of Service, attack is a type of cyberattack where an attacker attempts to make a machine or network resource unavailable to its intended users. This is typically accomplished by flooding the targeted machine or resource with superfluous requests, overloading systems and preventing legitimate requests from being fulfilled. As discussed in Cybersecurity 101, understanding the basics of DDoS is crucial in preventing and mitigating these types of attacks. For example, Network Security measures can help detect and prevent DDoS attacks.
What are the different types of DDoS attacks?
There are several types of DDoS attacks, each with its own unique characteristics and goals. Volumetric DDoS attacks, for example, involve inundating a server with millions of requests to slow its performance. On the other hand, Application Layer DDoS attacks target specific applications or services, attempting to overwhelm them with a substantial amount of invalid data. As explained in DDoS Protection strategies, understanding the different types of DDoS attacks is essential in developing effective defense mechanisms. Furthermore, Incident Response plans can help organizations respond quickly and effectively to DDoS attacks.
How can I prevent a DDoS attack?
Preventing a DDoS attack requires a combination of technical expertise and strategic planning. As discussed in DDoS Mitigation strategies, organizations can use various techniques, such as Traffic Filtering and Rate Limiting, to detect and prevent DDoS attacks. Additionally, Incident Response Planning can help organizations respond quickly and effectively to DDoS attacks. For example, DDoS Detection tools can help identify DDoS attacks in real-time, while DDoS Response plans can help organizations respond quickly and effectively to DDoS attacks.
What is the economic impact of a DDoS attack?
The economic impact of a DDoS attack can be significant, with some estimates suggesting that the average cost of a DDoS attack is over $1 million. As explained in DDoS Cost, understanding the economic impact of DDoS attacks is crucial in developing effective defense mechanisms. For instance, DDoS Insurance can help organizations mitigate the financial impact of DDoS attacks, while DDoS Risk Management can help organizations assess and mitigate the risk of DDoS attacks. Furthermore, Cybersecurity Investment can help organizations invest in cybersecurity measures to prevent and mitigate DDoS attacks.
What is the future of DDoS and cybersecurity?
The future of DDoS and cybersecurity is uncertain, but one thing is clear: the threat landscape is evolving rapidly. As discussed in Cybersecurity Trends, organizations must stay ahead of emerging threats, such as IoT Security and AI-Powered DDoS. For example, IoT DDoS attacks involve using IoT devices to launch DDoS attacks, while AI DDoS attacks involve using AI algorithms to launch DDoS attacks. Additionally, Quantum Computing can help organizations develop more effective cybersecurity measures to prevent and mitigate DDoS attacks.
How can I respond to a DDoS attack?
Responding to a DDoS attack requires a combination of technical expertise and strategic planning. As discussed in Incident Response plans, organizations can use various techniques, such as Traffic Filtering and Rate Limiting, to detect and prevent DDoS attacks. Additionally, DDoS Response Planning can help organizations respond quickly and effectively to DDoS attacks. For example, DDoS Detection tools can help identify DDoS attacks in real-time, while DDoS Response plans can help organizations respond quickly and effectively to DDoS attacks.
What is the role of cybersecurity in preventing DDoS attacks?
Cybersecurity plays a crucial role in preventing DDoS attacks. As explained in Cybersecurity Best Practices, understanding the basics of DDoS and developing effective defense mechanisms is crucial in preventing and mitigating these types of attacks. For instance, DDoS Prevention strategies can help organizations prevent DDoS attacks, while DDoS Response Planning can help organizations respond quickly and effectively to DDoS attacks. Furthermore, Cybersecurity Awareness can help organizations raise awareness about the importance of cybersecurity and the threat of DDoS attacks.